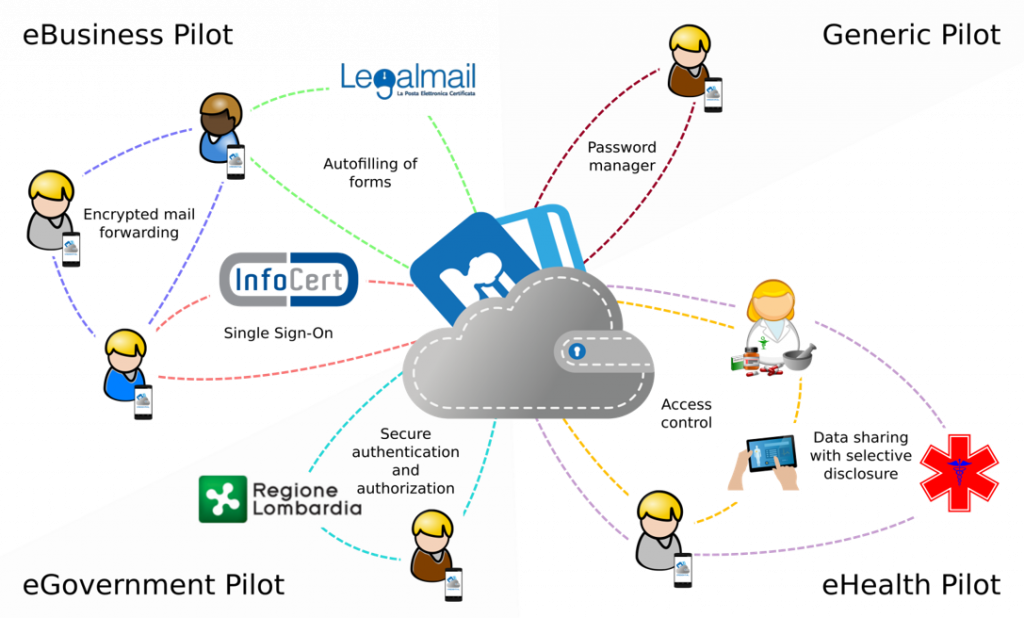
 Piloting and testing are integral parts of CREDENTIAL and a major focus during the third project phase. The deployment of developed CREDENTIAL tools on a European scale in a highly distributed environment with different stakeholder and user groups involved is a challenging task. The piloting and testing action aims to validate the technical and economic viability of the novel cloud based CREDENTIAL identity wallet in a near to operational environment. To evaluate and validate the capabilities of CREDENTIAL tools and bring developed components to market readiness, scenes for e-Government solutions, e-Health services and e-Business applications will be set up. Detailed piloting requirements and plans will be elaborated during the project.
Piloting and testing are integral parts of CREDENTIAL and a major focus during the third project phase. The deployment of developed CREDENTIAL tools on a European scale in a highly distributed environment with different stakeholder and user groups involved is a challenging task. The piloting and testing action aims to validate the technical and economic viability of the novel cloud based CREDENTIAL identity wallet in a near to operational environment. To evaluate and validate the capabilities of CREDENTIAL tools and bring developed components to market readiness, scenes for e-Government solutions, e-Health services and e-Business applications will be set up. Detailed piloting requirements and plans will be elaborated during the project.
e-Government
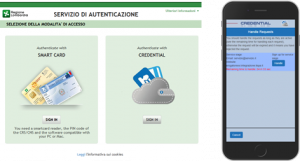 The eGovernment pilot considers citizens who wich to authenticate themselves towards services offered by public authorities using the CREDENTIAL Wallet as an identity provider.
The eGovernment pilot considers citizens who wich to authenticate themselves towards services offered by public authorities using the CREDENTIAL Wallet as an identity provider.
By doing so, the user receives full transparency over which personal attributes are revealed to the authority, and also remains assured that due to the deployed encryption technologies the CREDENTIAL Wallet does not gain access to the user's attributes.
More specifically, we consider a user who wants to authenticate himself towards SIAGE, a web portal used in the region of Lombardia hosted by LISPA, to request tax breaks and other financial advantages. Upon browsing to the default SIAGE login page, the user is given the option to choose CREDENTIAL as an identity provider, and is then redirected to an URL published by the OpenAM component in charge of initating the authentication flow according tot he OAuth2 standard. A notification on his mobile phone informs the user of the data SIAGE wants to access. If the user accepts this request, the CREDENTIAL Wallet re-encrypts the user's data and sends it to SIAGE, which can then decrypt the data and verify its authenticity.
The eGovernment use case also considers cross-border authentication according to the eIDAS regulation and aims at high interoperability with existing authentication protocols.
e-Health
This pilot realizes a se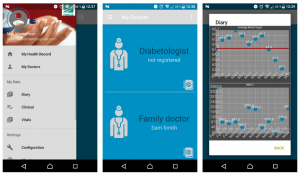 cure data sharing platform between doctors and patients, specifically focusing on the context of Type 2 Diabetes. Besides the necessary server-side components, this pilot implements two applications for patients and doctors, respectively. Patients can use their app to record health data such as blood sugar level, weight, or blood pressure using external devices. Besides giving patients visual representations of the collected data, this data is encrypted and stored securely in the CREDENTIAL Wallet. Patients may decide to grant doctors access to their data, in which case the app computes a re-encryption key and deposits it in the CREDENTIAL Wallet. When a doctor now wants to access the data, the CREDENTIAL Wallet re-encrypts the data and displays it to the doctor. Based on what they see, doctors can then provide feedback to the patients through the CREDENTIAL Wallet.
cure data sharing platform between doctors and patients, specifically focusing on the context of Type 2 Diabetes. Besides the necessary server-side components, this pilot implements two applications for patients and doctors, respectively. Patients can use their app to record health data such as blood sugar level, weight, or blood pressure using external devices. Besides giving patients visual representations of the collected data, this data is encrypted and stored securely in the CREDENTIAL Wallet. Patients may decide to grant doctors access to their data, in which case the app computes a re-encryption key and deposits it in the CREDENTIAL Wallet. When a doctor now wants to access the data, the CREDENTIAL Wallet re-encrypts the data and displays it to the doctor. Based on what they see, doctors can then provide feedback to the patients through the CREDENTIAL Wallet.
The deployed encryption technologies guarantee that no third party, including the CREDENTIAL Wallet hosting it, ever gets access to a patient's plain health data. Furthermore, we are investigating means to even hide meta data from the CREDENTIAL Wallet, as in certain cases access patterns to specific data could already allow an adversary to infer sensitive information about the data being stored.
e-Business
 CREDENTIAL's eBusiness pilot comes in three different flavors. The first scenario uses the CREDENTIAL as a Single Sign-On provider and is technically related to our eGovernment pilot. The second scenario helps the user in filling in personal data into online forms when registering for a new service, by transferring the encrypted user data from the CREDENTIAL Wallet to the service provider who is then able to decrypt and verify the data.
CREDENTIAL's eBusiness pilot comes in three different flavors. The first scenario uses the CREDENTIAL as a Single Sign-On provider and is technically related to our eGovernment pilot. The second scenario helps the user in filling in personal data into online forms when registering for a new service, by transferring the encrypted user data from the CREDENTIAL Wallet to the service provider who is then able to decrypt and verify the data.
The third use case is related to ICERT's Legalmail service, which realizes legally binding mail exchange; in particular, a mail is legally considered delivered once it reached the recipient's mailbox, independent of whether the recipient actually accesses the mail or not, and thus payment deadlines or objection periods start in the moment of delivery. The goal of CREDENTIAL is to add an end-to-end encryption layer to this service. However, due to the legal properties of Legalmail, it is important that emails can still be forwarded to a deputy in case of longer absences. This is not possible with standard public key encryption, as users would have to share their secret keys with the delegatee, or the sender would need to be notified and would have to re-send the mail again to the deputy. By integrating CREDENTIAL's proxy re-encryption libraries into the Legalmail mail server, users can now deposit re-encryption keys for a delegatee at the server, which can now re-encrypt the mails to the new recipient without leaking the mail's content to the mail server.
